How to configure Tableau SAML SSO with Salesforce Identity IdP(and some key gotchas)
(Edit: 16 Aug 2021 — There’s an easier way nowadays to implement Salesforce as an SSO IDP for Tableau Online that doesn’t rely on SAML, but rather OpenID Connect. You can read more about it here. This article is still valid, should you prefer to use SAML. NB: my personal preference is SAML, read more why at the bottom of this article).
The process to configure Salesforce as Single Sign-on IdP for Tableau Online (or Tableau Server) can be super frustrating and difficult to debug.

In this short video, you’ll see a step-by-step and the main gotchas you might encounter when trying to integrate this method of Authentication to your Tableau Online and Salesforce Connected App.
You’ll also see in action some of the tools I use to troubleshoot eventual SAML configuration errors. Namely these are:
- Downloading logs from Tableau Online SAML config
- Inspecting Salesforce Identity Event Logs
- Chrome add-on — SAML Message Decoder
Last, but not least, this blog post has loads of gotchas you really ought to be aware of (not all mentioned in the video).
Buckle up and enjoy!
The official Guide from Tableau on how to configure this can be found here.
Some additional gotchas worth noting (not all mentioned in the video):
a) Since Jan 21, Tableau Online requires messages to be signed with SHA-256 hash algorithm, as opposed to SHA-1. Make sure to configure your IdP (SF SAML config) accordingly.
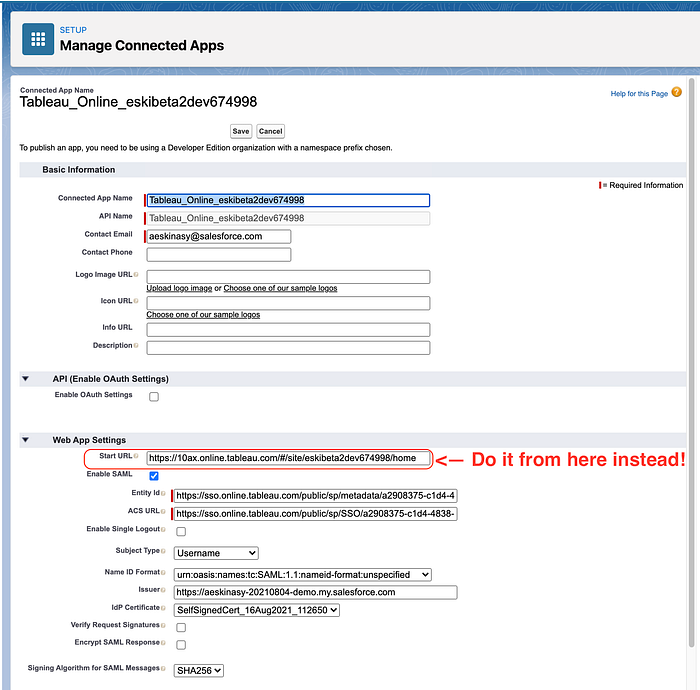
b) If you are following my video and can’t get the SSO config in Tableau Online, try to change the “Start Url” on of your Connected App setting in Salesforce following this pattern:
https://us-west-2b.online.tableau.com/#/site/your-site/home
as opposed to:
https://us-west-2b.online.tableau.com/#/site/your-site ←not in use anymore!
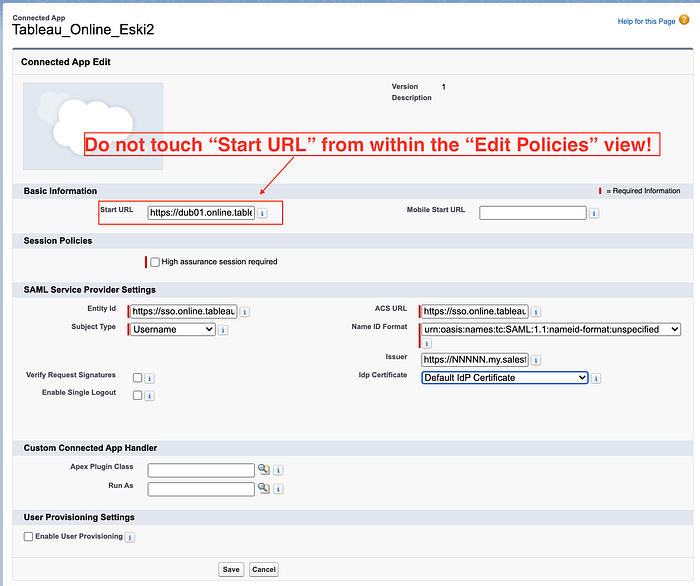
c) Additionally, Do not change the “Start Url” from within the “Edit Policies” screen, as it seems to trigger some unknown bug that may corrupt this Connected App!
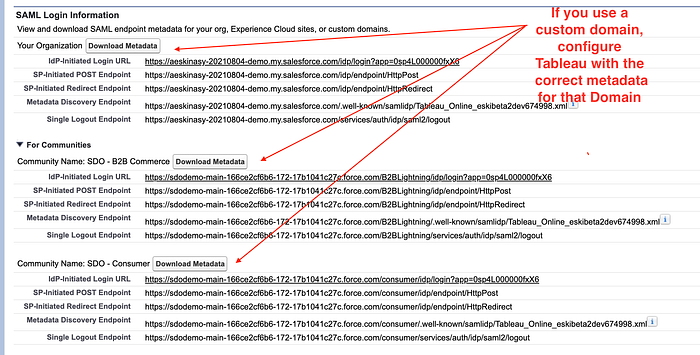
d) If the SSO is used on a specific Community Portal that runs under your own custom domain, make sure to use the apporpriate metadata file when configuring SAML on your Tableau Online/Server
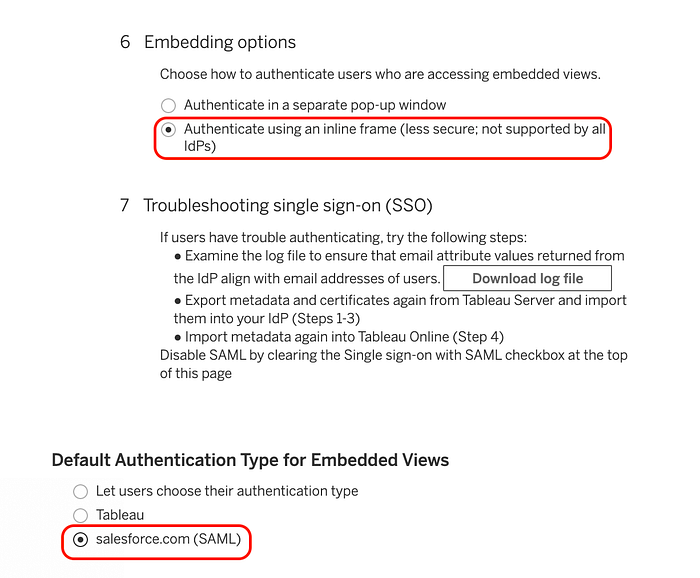
e) When embedding Tableau views, make sure to enable the following two settings (Authenticate using an iframe and set the default authentication type for embedded views to be SAML):
f) If you are running into CSP (Content Security PoLicy) issues, add your domain as trusted as follows:
- In Salesforce go to Setup → Security → CSP Trusted Sites
- Add an entry for https://*.tableau.com (this will whitelist Online and Public).
- For Tableau Server add an entry for the server = https://*.{Tableau Server Domain}. The * is a wildcard to capture all entries with that domain.
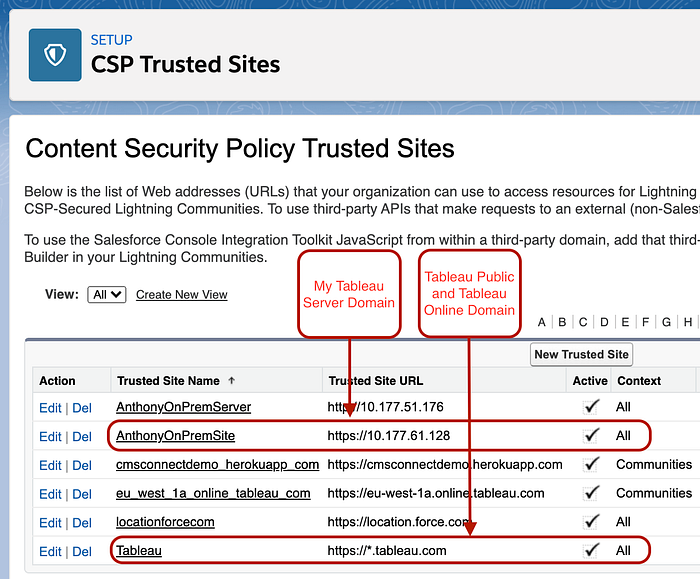
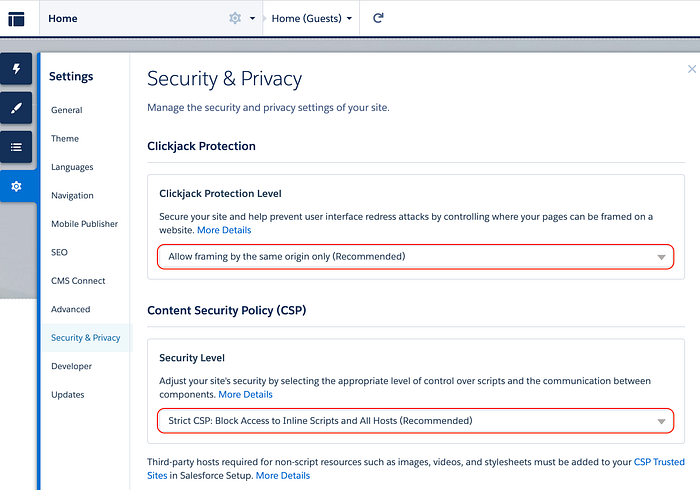
g) If you are embedding Tableau on a Community page, you may leave the CSP and Clickjacking settings as default and most restrictive, as the CSP configuration from Salesforce mentioned above is alreadying taking care of it through “Context = All”:
h) Integration with Tableau Server is not very different:
- Make sure to enable SSL, even if it is a self-signed certificate. Salesforce will offload to SSL by default, so you’ll be in trouble if not. Note: it’s still technically possible in HTTP, but requires some cumbersome settings on Salesforce side. If you happen to need help installing a Self-Signed cert on your Tableau Server instance (for testing purposes), feel free to follow my quick tutorial.
- If you plan to use Server-Wide SAML, enable it with the following commands (you can use your self-signed cert here):
tsm authentication saml configure --idp-entity-id <tableau-server-entity-id> --idp-return-url <tableau-server-return-url> --cert-file <path-to-saml-certificate.crt> --key-file <path-to-saml-keyfile.key>- Here, make sure — idp-entity-id <tableau-server-entity-id> is HTTPS Protocol!
i) Additional steps to enable Site-Specific SAML on Tableau Server:
tsm authentication sitesaml enable
tsm pending-changes applyAll information on Site-Specific SAML can be found here.
Hope this is useful to some of you :D
Should I use SAML or Salesforce for SSO?
As mentioned at the top of the article, there’s now a new option for SSO leveraging OpenID Connect protocol which is WAY EASIER to configure, as opposed to SAML:

Both have their own merits, but in my opinion SAML provides a superior experience for Embedded views, because end-users will never guess that embedded visualizations are coming from a different system (Tableau).
On the other hand, the new “Salesforce” method, requires end-users of your portal to authenticate with Tableau Online (once only), whenever they land on a page that contain an embedded view. From an end-user perpective, knowing that they will be sharing their data with a third-party system (i.e. Tableau) might be interesting to know from a security perspective, however I think more often than not Portal owners will not want their users to know the Analytics content is coming from a different system, as it might not feel properly whitelabeled. Nevertheless, perhaps such flow is relevant to fullfil a compliance requirement.
While setting up SAML can be painful, it’s really a one-time effort to go through, as the final end-use experience is really great, end-users can’t really tell vizzes are coming from Tableau.
I’d love to know which SSO method is your favourite, so share in the comments below!
